Most security decisions in IT are invisible. BIMI is unusual because it is one of the few email-security signals that can surface directly in the inbox — but only after the underlying authentication foundation is already operating correctly.
Most security decisions in IT are invisible.
They live quietly inside DNS records, authentication headers, and policy enforcement rules that most users will never see.
Email security is no exception.
SPF, DKIM, and DMARC work behind the scenes to verify that a message truly came from the domain it claims to represent. When configured correctly, these systems dramatically reduce spoofing and impersonation attacks.
Recently we took the additional step of preparing our own domain for BIMI — Brand Indicators for Message Identification.
BIMI is interesting because it is one of the few email security standards where the result can actually appear in the inbox.
Sometimes, when a message arrives, the sender's logo appears next to the message.
That logo is not marketing decoration. It is the visible signal that several layers of email authentication are functioning correctly underneath.
What BIMI Actually Is
BIMI allows a domain owner to publish a DNS record that points to a verified version of their brand logo.
When an email provider supports BIMI and trusts the domain's authentication posture, the mailbox interface may display that logo next to authenticated messages.
But BIMI itself is not the core security control.
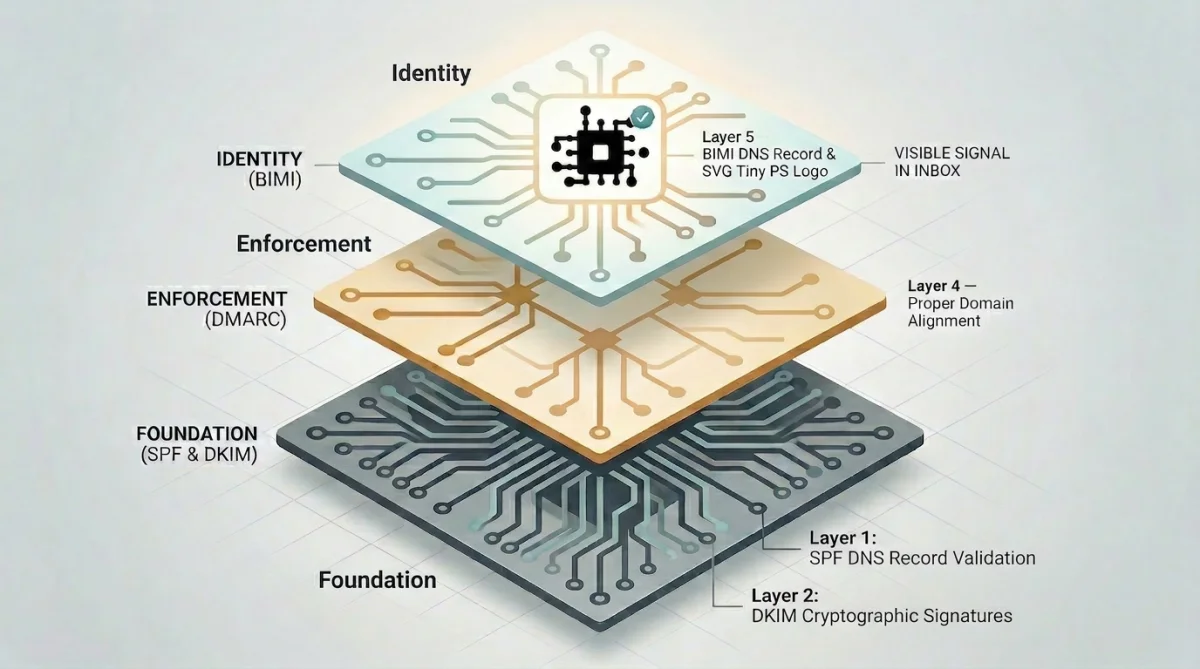
Instead, it sits on top of several existing identity mechanisms:
- SPF validation
- DKIM cryptographic signatures
- Strict DMARC enforcement
- Proper domain alignment
- A properly formatted SVG Tiny PS logo
By the time a domain can successfully publish a valid BIMI record, the underlying authentication system must already be operating correctly.
In other words, BIMI is more of a visible checkpoint than a standalone feature.
Our Domain's Current BIMI Status
We recently published a BIMI record for our domain and validated that it passes standard record checks.
This means the authentication foundation underneath it is working as expected:
- SPF and DKIM are aligned
- DMARC is operating in enforcement mode
- The required BIMI record and logo format are valid
Some mailbox providers can already make use of that information.
For example, in Apple's iCloud Mail, our logo may appear alongside authenticated messages.
Other providers apply additional requirements.
Gmail, for example, typically requires a Verified Mark Certificate (VMC) issued by a certificate authority before displaying a logo. We have not purchased that certificate layer at this time, so Gmail currently does not display the logo for our domain.
That distinction matters.
The BIMI record itself is valid and published. The remaining step for broader display is the certificate-based trust layer used by certain providers.
Why the Preparation Matters
The interesting part of BIMI is not the logo.
The interesting part is what must already be true before the logo becomes possible.
For BIMI to function at all, a domain must already have implemented strict DMARC enforcement.
DMARC policies generally fall into three categories:
p=nonep=quarantinep=reject
The first option monitors authentication failures but does not enforce any action.
BIMI requires a domain to move beyond monitoring and into enforcement. In practice that means publishing a policy of either:
p=quarantinep=reject
That shift represents a significant step in email identity maturity.
It means a domain owner has reached a level of confidence in their authentication configuration where spoofed messages should be actively handled rather than simply observed.
The Email Identity Gap
Most of the systems that protect email identity operate quietly.
A recipient cannot normally see whether SPF passed, whether DKIM aligned, or whether DMARC policy enforcement occurred.
BIMI is unusual because it exposes the result of that work in a way a human can immediately recognize.
The appearance of a verified logo is not the security control itself.
It is the visible signal that the invisible controls were implemented correctly.
Why We Did the Work
Preparing a domain for BIMI was not about adding a logo to an inbox.
It was about completing the identity work that makes modern email systems trustworthy.
Email spoofing remains one of the simplest ways to impersonate an organization online. Strong authentication policies dramatically reduce that risk.
Publishing and validating a BIMI record simply confirmed that our domain's authentication posture supports the next level of identity verification.
Whether or not every provider chooses to display the logo is secondary.
The important part is that the underlying identity system is operating correctly.
Quiet Infrastructure
At Enuclea we spend most of our time on systems that users never see.
Clean DNS records.
Aligned authentication.
Infrastructure that behaves predictably and quietly in the background.
BIMI happens to expose a small piece of that work to the outside world.
But the real value was never the logo.
The value was the foundation underneath it.
If you'd like a calm read on how your own domain is presenting itself, start with a free Email Security Check or request an Email Baseline Review.
Run your domain's email check
SPF, DKIM, DMARC — scored and explained in 30 seconds.
Run Free Email CheckRelated Resources
- Professional Email Services — Domain-based email with verified identity
- Business Email Startup — $250 — Microsoft 365 setup with SPF, DKIM, DMARC
- Managed IT in Stafford, VA — Monitoring, patching, MDR, and support
- Case Studies — See how we've helped businesses like yours
- All Services — IT support, network design, and security