Many organizations invest heavily in inbound security—filtering gateways like Barracuda or Proofpoint—while neglecting the outbound "Infrastructure Authority" that dictates how the rest of the world perceives them. This report analyzes a real-world entity with high-end filtering but a Maturity Score of 60/100, illustrating how internal DNS gaps create financial and reputational risk.
I. The "Cornerstone" Fallacy
A common misconception is that a secure gateway (Inbound MX) equals a secure domain.
Case Study Infrastructure
Inbound Gateway: d296763a.ess.barracudanetworks.com
While this protects what comes in, it does nothing to authenticate what goes out to clients, partners, and vendors.
The Risk
Without outbound identity alignment, the organization's invoices, proposals, and communications are effectively sending blind. Modern corporate filters evaluate sender identity before content ever matters.
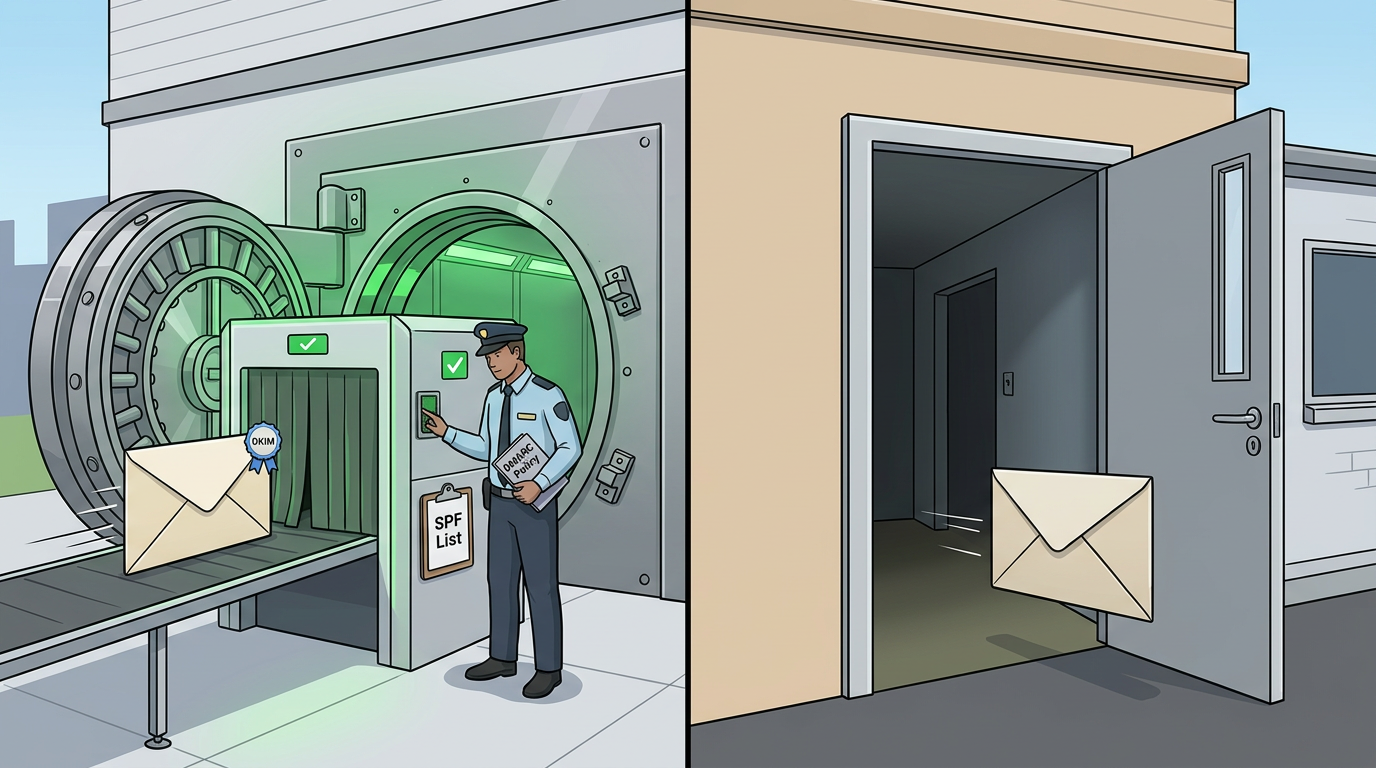
II. The Three Pillars of Identity
Even with an expensive gateway, three specific technical failures create a "Visibility Gap".
1. The Missing Security Guard (DMARC)
Finding: No DMARC policy found.
Impact: Spammers can freely impersonate the domain. The organization has zero visibility into who is attempting to send mail on its behalf.
Without DMARC:
- No reports on authentication failures
- No protection against domain spoofing
- No enforcement mechanism for SPF/DKIM
2. The Missing ID Badge (DKIM)
Finding: No DKIM selectors found. Emails lack cryptographic authentication.
Impact: Even if a "pass" occurs on the guest list (SPF), the message lacks the digital signature modern mail systems use to validate legitimacy.
DKIM provides:
- Cryptographic proof the message wasn't altered in transit
- Verification that the sender controls the domain
- Protection against content tampering
3. The Reverse DNS Mismatch
Finding: The PTR record exists but does not match the MX hostname.
Impact: High-security receiving servers see this mismatch as a reduced-trust signal. In many environments this causes mail to default to spam or junk folders.
III. The Financial Risk
When identity maturity is low, the risks move beyond "spam annoyance" into real operational impact.
Invoice Visibility
Proposals and invoices may land in spam folders, delaying accounts receivable.
Wire Fraud Risk
Without cryptographic signatures (DKIM), outbound messages can be intercepted or altered without the recipient knowing the content was modified.
Shadow Reputation
Using a strict SPF policy (such as -all) without ongoing management can cause legitimate new systems—CRM tools, marketing platforms, or automation software—to fail silently.
IV. The Infrastructure Authority Score
Email trust is evaluated across two dimensions: identity authority and infrastructure trust.
Identity Authority (85 points possible)
- Domain Identity (35 pts) - Custom domain vs. free-mail
- SPF Authentication (15 pts) - Authorized sender list
- DKIM Cryptographic Signing (10 pts) - Message integrity
- DMARC Policy Enforcement (25 pts) - Spoofing protection
Infrastructure Trust (15 points possible)
- Reverse DNS Alignment (15 pts) - PTR/MX consistency
Together these signals produce an Infrastructure Authority Score out of 100, reflecting how receiving mail systems evaluate the legitimacy of a sender.
V. The Real-World Impact
Consider this scenario:
A company with Barracuda filtering sends a $50,000 proposal to a Fortune 500 prospect. The prospect's mail system sees:
- ❌ No DKIM signature
- ❌ No DMARC policy
- ⚠️ Reverse DNS mismatch
Result: The proposal lands in spam. The prospect never sees it. The deal goes to a competitor.
The cost of the lost opportunity far exceeds the cost of proper DNS configuration.
VI. Conclusion
A healthy configuration requires more than an inbound filtering gateway.
True email trust requires:
1. Verified Identity
SPF, DKIM, and DMARC fully implemented and aligned.
2. Infrastructure Authority
Mail infrastructure that aligns with the sending domain.
3. Ongoing Monitoring
DMARC policy progression from monitoring to enforcement.
The Bottom Line
Organizations that invest in filtering without addressing identity leave a critical gap in their communications infrastructure.
Modern email systems evaluate identity first. Without it, even expensive filtering gateways cannot prevent reputational damage or operational loss.
Want to know your organization's Infrastructure Authority Score?
Run a Free Email Security Check →
Our tool analyzes your domain's SPF, DKIM, DMARC, and Reverse DNS configuration in seconds—no signup required.
Run your domain's email check
SPF, DKIM, DMARC — scored and explained in 30 seconds.
Run Free Email Check